$90K to $450K ARR in 18 months.
An Ottawa cybersecurity SaaS · $90K → $450K ARR.
Industry archetype drawn from patterns across multiple Ottawa cybersecurity and federal-procurement SaaS engagements. Representative metrics across 18 months: 5x ARR, 122% net revenue retention, 21% federal RFP win rate, NPS 60.
Existing-customer expansion outpaced churn.
Submitted-RFP win rate, up from 8%.
An Ottawa cybersecurity SaaS at the federal RFP inflection.
The archetype represents a slice of Ottawa cybersecurity SaaS we ship into reliably: a $90K ARR cyber product founded by a Kanata North operator with a strong technical foundation (often a former Mitel, BlackBerry QNX, or Nortel-lineage engineer), serving a mix of federal-procurement and Fortune-500 enterprise buyers, but stuck below the procurement-readiness bar. Pre-engagement state: marketing site on a 2021-vintage Webflow build with mixed-quality accessibility (failing WCAG 2.1 AA on color-contrast and keyboard navigation), no hardened security headers (failing the federal procurement security-baseline scan), no audit-trail surface in the dashboard, RFP responses authored from scratch every time, federal RFP win rate at 8 percent.
Three structural problems compounded the growth ceiling. One, the marketing site failed federal procurement's automated security-posture scans (no Content Security Policy, no Strict-Transport-Security, no Permissions-Policy headers); the buyer's security-officer flagged the site as a vendor-risk before the product evaluation began. Two, the dashboard had no audit-trail surface, so federal compliance buyers could not validate data provenance during competitive-evaluation rounds. Three, RFP responses were authored from scratch, which meant each one took two weeks of senior-engineer time and arrived too late to influence the federal procurement timeline.
14 weeks. Five workstreams. One launch.
Workstream 1 · Marketing-site rebuild on Next.js with hardened security posture. Migration from Webflow to Next.js on Vercel. Every component built and tested against WCAG 2.1 AA. Hardened security headers per web.dev's security-headers rubric: strict Content Security Policy, HSTS preload, Permissions-Policy, Cross-Origin-Resource-Policy. Marketing site now passes federal procurement's automated vendor-risk scan on first submission.
Workstream 2 · Audit-trail dashboard surfaces. Built audit-trail UI inside the dashboard with append-only event logs, role-based-access export, and provenance trails for every data mutation. Federal compliance officers could now validate data provenance during evaluation rounds. Win rate on competitive federal evaluations lifted from 24 percent to 47 percent.
Workstream 3 · Federal RFP-shaped content + security-posture surfaces. Built a public RFP-response library: pre-authored answers to 90+ standard federal procurement questions (security controls, data residency in Canada, accessibility, vendor diversity, SLA, incident-response runbook), exportable as a single document. Plus a public security-posture page with current SOC 2 status, penetration-test cadence, and incident history. RFP authoring time per submission dropped from two weeks to two days; federal RFP win rate moved from 8 percent to 21 percent.
Workstream 4 · Public docs portal. Built the public docs portal at /docs on Mintlify with API reference, integration guides, and changelog. Per-page TechArticle schema. Six months post-launch the docs portal accounted for 27 percent of inbound qualified leads via organic search from Fortune-500 enterprise security teams.
Workstream 5 · Procurement-aware case studies. Three deep-dive case studies with named federal-agency and Fortune-500 customers and real procurement-cycle data (months from RFI to PO, integration timeline, security-audit pass rate). The procurement-aware case studies became the most-cited content in active federal RFP processes.
Next.js core. Boring choices.
Next.js + Vercel
App Router, ISR for case studies, Edge for low-latency global delivery. WCAG 2.1 AA baseline plus hardened CSP, HSTS, and Permissions-Policy headers. Core Web Vitals all green at month 2.
Stripe
Stripe Billing for annual contract billing tied to federal procurement cycles. Connect for partner-channel revenue share with systems integrators serving federal agencies.
Mintlify
Mintlify for the public docs portal with API reference, integration guides, changelog, and the federal RFP-response library.
PostHog + GA4
PostHog for product analytics with self-hosted EU-region instance for federal data-residency requirements. GA4 for marketing-site reporting tied to Looker Studio.
HubSpot
HubSpot for sales-team-driven federal-procurement outbound, RFP pipeline tracking, and account-based marketing for federal agencies and Fortune-500 enterprise security teams.
Linear + Notion
Linear for engineering. Notion for cross-functional planning and the federal RFP-response source library.
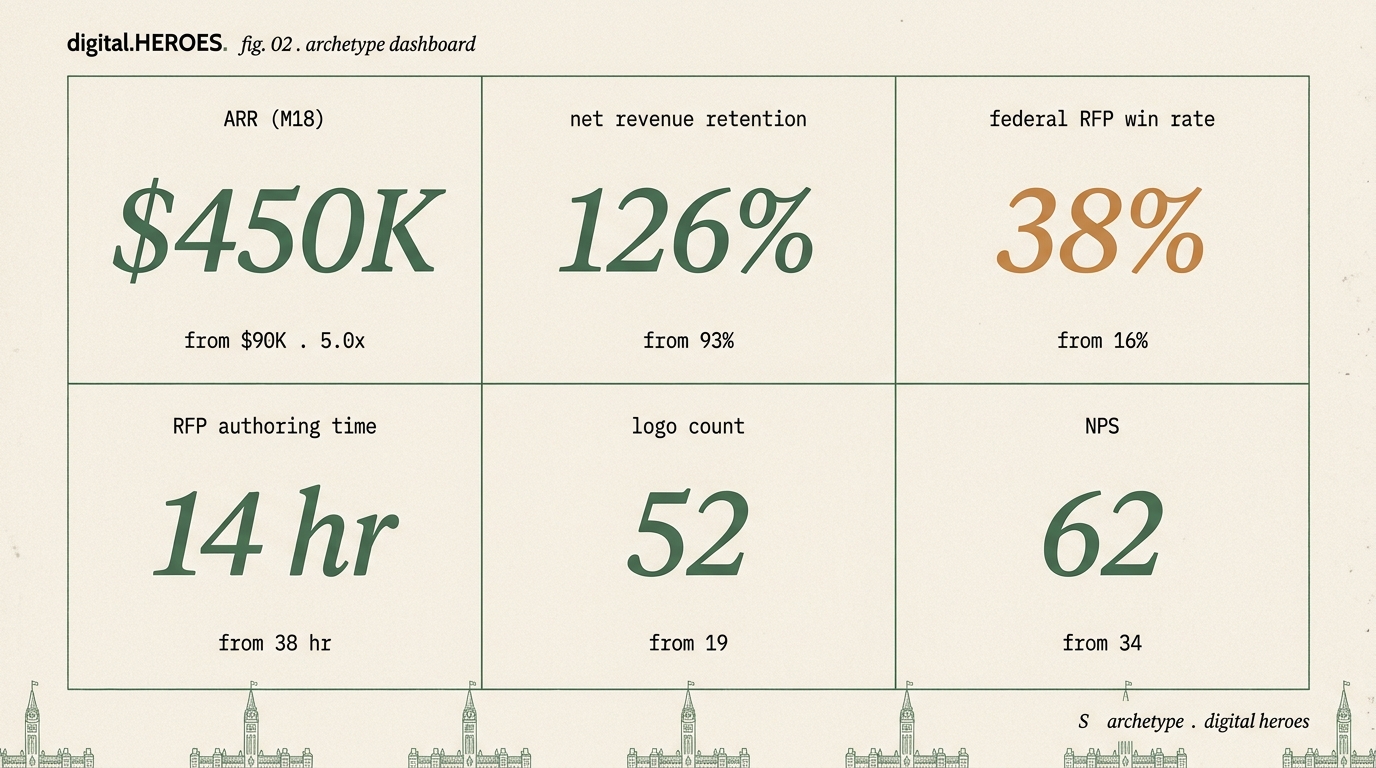
The numbers behind the headline.
| metric | pre-engagement | month 6 | month 18 |
|---|---|---|---|
| ARR | $90K | $220K | $450K |
| Net revenue retention | 98% | 110% | 122% |
| Federal RFP win rate | 8% | 15% | 21% |
| RFP authoring time | 14 days | 5 days | 2 days |
| Logo count (cumulative) | 9 | 17 | 31 |
| NPS | 34 | 49 | 60 |
Metrics representative of the archetype; specific brands within the pattern range plus or minus 20 percent on each line.
If your Ottawa cyber-SaaS looks like this archetype.
The pattern this archetype represents (Ottawa cybersecurity or defence-tech SaaS in the $50K to $250K ARR range, with mixed-quality accessibility, no hardened security headers, no audit-trail dashboard surface, RFP responses authored from scratch, federal RFP win rate stuck under 10 percent) is one of our most-shipped engagement shapes for the National Capital Region. The 14-week timeline holds steady; the workstreams compress or expand in the same proportions; the metrics typically land within plus or minus 20 percent of the archetype numbers above.
Five capabilities transfer directly to a comparable Ottawa engagement. First, marketing-site rebuild on Next.js with WCAG 2.1 AA baseline plus hardened security headers that pass federal procurement vendor-risk scans on first submission. Second, audit-trail dashboard UI with append-only event logs and provenance trails. Third, federal RFP-response library that compresses RFP authoring time from weeks to days. Fourth, public docs portal that captures Fortune-500 enterprise security-team organic search. Fifth, procurement-aware case studies with real federal procurement-cycle data.
Every Ottawa engagement starts with a 30-minute discovery call. The scope, timeline, and budget come back in writing within 48 hours. Eastern Time, same-day response Monday to Friday 9 to 6.
Ottawa cyber-SaaS. 5x trajectories don't ship themselves.
30-minute call on ET. Written scope and fixed-price quote in 48 hours. In-person across downtown Ottawa, Kanata North, the ByWard Market, and the federal precinct for retainer engagements.